For businesses transacting in the UK, there are many regulations that apply when using an electronic device to communicate. The UK General Data Protection Regulation (UK GDPR), or the Data Protection Act 2018, the Privacy and Electronic Communications Regulations (PECR) which sit alongside the Data Protection Act and the less obvious ones like the Company, Limited Liability Partnership and Business (Names and Trading Disclosures) Regulations 2015, which lays out requirements for information that must me included in your communications.
- Guide to the UK General Data Protection Regulation (UK GDPR) | ICO Data Protection Act 2018 (legislation.gov.uk)
- Guide to Privacy and Electronic Communications Regulations | ICO The Data Protection, Privacy and Electronic Communications (Amendments etc) (EU Exit) Regulations 2020 (legislation.gov.uk)
- The Company, Limited Liability Partnership and Business (Names and Trading Disclosures) Regulations 2015 (legislation.gov.uk)
These give people specific privacy rights and obligations in relation to electronic communications. Also be mindful of the provisions inside the companies act of record keeping and disclosure. As an information owner, you're responsible for managing your organisation's security risks and fulfilling your lawful requirements with things like disclosure in business communications from the companies act (like having legal email signatures) and retaining of email records.
IASME Cyber Assurance Is Available In Two Levels
Verified Assessment and Audited
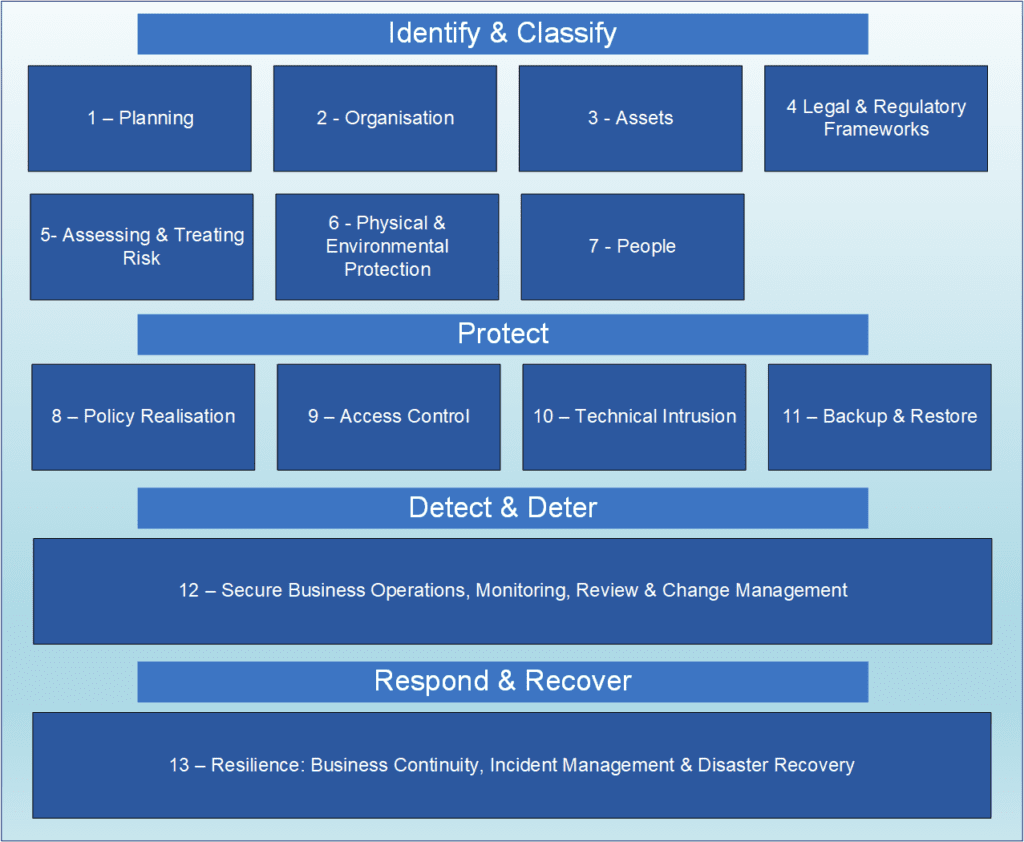
The IASME Cyber Assurance certification includes GDPR requirements and is available in two levels: Level 1 Verified Assessment and Level 2 Audited. There is a prerequisite to applying for IASME Cyber Assurance; you must hold a valid Cyber Essentials certificate throughout your IASME Cyber Assurance certification.
It is a great fit for organisations that want ISO 27001, but realise it's a long journey and use IASME as a significant stepping stone towards ISO 27001, as shown below there a mappings from Cyber Assurance to these other standards, meaning that the work is reusable towards those standards.
For Level 1 - verified assessment, organisations access a secure portal to answer around 160 questions about their security. The assessment is marked by a Certification Body and a pass or fail is returned to the organisation. For Level 2 - audited, an independent assessor conducts an on-site audit of the controls, processes and procedures covered in the IASME Cyber Assurance standard. The audited version gives a higher level of assurance and is pass or fail.
The Government's Procurement Bill 2022 is passing through the parliamentary process and is due to come into law. It seeks to reform the UK's public procurement regime to create a fairer and more transparent system. It also aims to support businesses by making public procurement more accessible to small businesses, and voluntary, charitable and social enterprises, by enabling them to compete for public contracts. Over 95% of all organisations in the UK are SMEs, many of whom are the most innovative organisations in their sector. The new procurement bill is a positive sign that SMEs are being welcomed and encouraged into supply chains and allowed to compete with larger organisations for business.
A wide range of industry sectors now accept the audited IASME Cyber Assurance certification as an alternative to ISO 27001 for small companies. This is a significant step towards reducing barriers to entry for smaller organisations in a supply chain as IASME Cyber Assurance gives SMEs a legitimate way to prove their compliance.
IASME Cyber Assurance maps to the majority of the ISO27001 / ISO27002 controls at achieved or partially achieved level, the mapping between IASME Governance and ISO27001 can be found here
The UK General Data Protection Regulation (GDPR) sets out seven key principles that should lie at the heart of an approach to processing personal data. Accountability is the seventh principle and the one that demonstrates that businesses are doing the right thing. IASME cyber Assurance aligns with the vast majority of the ICO's Accountability Framework, the mapping between IASME Governance and the ICO's Accountability Framework is here
Originally published in 2012 and is now used by a majority of the FTSE350 aligns directly with 10 Steps to Cyber Security on all topics, the mapping between IASME Governance and the 10 Steps Guidance is available here
The mapping between IASME Governance and the Network & Information Systems Regulations (NIS) Cyber Assessment Framework (CAF) can be found here


ISO 27001
ISO 27001 is the leading international standard for information security. Over 44,000 organisations all over the world use ISO 27001 to protect their data. The basic goal of the certification is to protect three aspects of information:
- CONFIDENTIALITY. Only authorised people have the right to access information
- INTEGRITY. Only authorised people can change the information
- AVAILABILITY. The information must be accessible to authorised people whenever it's needed
Don't look at ISO27001 and Cyber Essentials as somehow equivalent. They complement each other very well and don't directly overlap. ISO27001 focuses more on process controls and policy positions, with some practical assessment. Cyber Essentials is the opposite - the focus is much more on practical assessment, with some process and policy assessment.
Successful implementation of ISO 27001 requires careful planning and project management. Unlike the checklist-style of Cyber Essentials, ISO 27001 is an interlocking framework of policies and processes. So, you'll need to create process documents and maintain mandatory records of training, internal audits, and more.
Statius Management Services Ltd is a management consultancy company that we work closely with, and whose aim is to implement ISO management systems along side our technical deployments, that improve business efficiency and minimise disruption. Obtaining ISO 27001 is about systematically and rigorously testing your information security processes is against the 100+ controls detailed in Annex A of the standard.



